Yesterday, in part 1 of this article, we started doing a quick security checkup on Google accounts. If you have Gmail, an Android device, or use Google Drive, YouTube, or Google Chrome, you have a Google account. We showed you how to check for any authorized log in or pressing security issues. (Click here to read that article.)
We’ll continue that look by checking up on your Sign-in & recovery options.

This safeguard can protect you from unauthorized individuals logging into your account and also gives you several methods to recover that account should you forget the password.
I’ve selected four recovery methods. A phone number, an alternate email to my Gmail address, a security question, and a trusted mobile device where notifications can be I pushed. You can click the pencil icon to edit the phone number and email address. I suggest having as many verification methods as possible.

Next, you can click on Third-party access. This shows you how many apps have access to your Google information.

There are 11 apps with access to my information. Let’s talk about what they are and why they have that access. The first three apps have access to Gmail to allow me to share documents with my Gmail document. Mozilla Thunderbird is an email client, that must have access to Gmail to download my messages.

OS X has access because I use my Google Drive, Gmail, and Calendar on my Mac laptop. Photos has access because I back up photos taken on my phone to Google Photos. Samsung My Files has access because I sometimes open Google drive files and Google photos on my phone. Unroll me has access because it scans my inbox for newsletters I haven’t opened. Two Dots has access to Google Play because it’s an Android app.

Windows has access since I use the Gmail calendar, Gmail, and my Google contacts on my PC. The YouTube app on my Xbox has access because I log in so I can play my saved playlists on my TV.
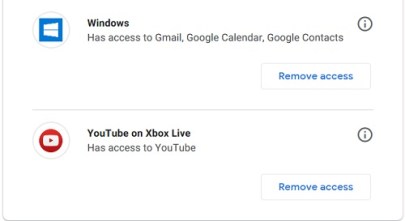
While I’m good with these permissions, if I saw one I didn’t authorize or just don’t feel I need anymore, I can click Remove access. Access will be gone in a flash.
One of the most important things you can do to protect your account is to turn on two-step verification. Tomorrow in part 3 of this series, I’ll show you how to do it for your Google account.